Arguments against systemd
From Without Systemd
Contents |
Links
- systemd: Please, No, Not Like This (October 2017)
- EWONTFIX - Broken by design: systemd
- Lamest Vendor Response 2017 #PwnieAwards goes to Lennart Poettering for SystemD f*ckups photo
- Patrick's playground - systemd propaganda: It's a crap!
- Top 5 systemd troubles - a strategic view for distros
- Systemd? More like Shit-stemd
- The bad side of systemd: two recent systemd failures
- There are several problems with systemd unrelated to code quality..."
- systemd: The Biggest Fallacies
- Fast boot? in-the-wild discussion (workarounding slow OOTB systemd boot) "Performance tuning the boot process"
- systemd: Assumptions, Bullying, Consent
- Open letter to the Linux World
- systemd pitfalls (July 2017)
- systemd Or Poettering, Name Your Poison
- Combatting revisionist history
- Local copy of boycottsystemd archive
- Ts’o and Linus And The Impotent Rage Against systemd
- A realization that I recently came to while discussing the whole systemd controversy...
- systemd vault - Everything you need to fully understand the systemd problem
- Systemd Forward Secure Sealing of System Logs Makes Little Sense
- journald and rsyslog
- What I don't like about journald / Linux Journal
- Disappointing press reactions...
- Why I dislike systemd
- Is `systemd` an NSA attempt?
- Systemd is the best example of Suck (suckless.org) "There is a menace which is spreading like a disease throughout the Linux world, it is called systemd."
- Structural and semantic deficiencies in the systemd architecture for real-world service management, a technical treatise
- PAPPP's ramblings - Linux Future (how systemd is not like Unix)
- Systemd requiring CAP_SYS_ADMIN weakening container safety in coreOS/rkt
- Problems with Systemd and Why I like BSD Init by Randy Westlund
- ubuntubsd.org article titled "Why Systemd is so bad?"
- The reasons why I hate systemd
- Debian Bug #668001 "debootstrap: cant install systemd instead of sysvinit" (2014 mailing list thread, 100+ msgs)
Breaking promises and immaturity
Linux (kernel) coup attempt: "kdbus support is no longer compile-time optional ... We encourage all downstream distributions to begin testing kdbus by adding it to the kernel images in the development distributions, and leaving kdbus support in systemd enabled." comment on this on LKML
"kdbus dropped in favor of BUS1"
Stability Promises
To quote from the systemd stability promise:
- "Starting with version 26 (the first version released with Fedora 15) we promise to keep a number of them stable and compatible for the future."
One of their promises is for the export format:
- "Entry metadata that is not actually a field is serialized like it was a field, but beginning with two underscores. "
This is not true for version 44 of systemd for example.
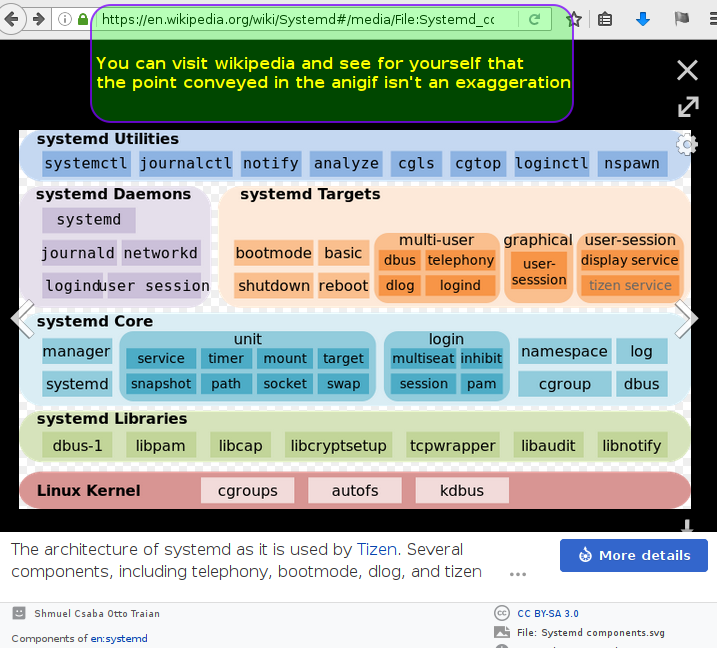
Scope creep
- systemd assimilates udev
- systemd takes over logging (and as if that wasn't bad enough, it uses a binary format)
- Systemd Gains IP Forwarding, IP Masquerading & Basic Firewall Controls
- Gummiboot UEFI Boot Loader To Be Added To Systemd
- DNS cache --- systemd-resolved
- web server
- Systemd developer asks tmux to add systemd specific code
- An init system that requires even on a server a library for rendering QR codes: Post in Heise Forum and reference in Fedora
- Systemd assimilates mount
Absurd Bugs and Responses
- Unchecked null pointer dereferencing in PID 1 not considered a serious issue - "To make this work we'd need a patch, as nobody of us tests this.", "I will not work on this" - Systemd requires cgroups and segfaults if there is no cgroups support.
- Screen locking issues (including a security issue) with gnome-shell - remained unfixed for over a year]
- PID 1 segfaulting on upgrade; journalctl usability issue - bug report still marked as "NEW"
- "Tried to boot my laptop from a cafe..."
- systemd segfaults after updating from 208-23.3 to 208-28.1
- Mount efivarfs read-only - Doing rm -rf / bricks your computer
- Unable to shutdown
- journald eats up CPU
- Corrupted binary logs
- How to Crash Systemd in One Tweet (works as any user, not just root) and response and rebuttal
- Systemd v228 local root exploit
- tmpfiles: R! /dir/.* destroys root See also systemd again (or how to obliterate your system), Poettering's response: "I am not sure I'd consider this much of a problem. Yeah, it's a UNIX pitfall, but "rm -rf /foo/.*" will work the exact same way, no?" (Hint: no.)
- systemd can't handle the process previlege that belongs to user name startswith number, such as 0day Poettering: "not a bug, a feature"
- systemd Using 4GB RAM After 18 Days of Uptime
Conceptional problems
- Systemd Prevents the Skipping of fsck while Booting - still unresolved
- Systemd Disables the Linux Magic SysRq Key - closed as "NOTABUG"
- Please do not default to using Google nameservers - Debian package maintainer refuses to acknowledge the privacy leak and closed the bug.
- timeX.google.com provide non standard time - Horrible default behaviour but Lennart tries to shift the blame on distros because "systemd is not a product".
- Do not parse "debug" command line parameter - Response on LKML Response: That is the expected current behaviour, "debug" can cause "too many" messages to be useful anymore if things are broken.
- journal ip anonymization - It's very difficult to use systemd/journal on a privacy aware system or infrastructure.
- systemd kill background processes after user logs out - Poettering's answer: In my view it was actually quite strange of UNIX that it by default let arbitrary user code stay around unrestricted after logout.
- systemd-resolved is broken - doing DNS resolve wrong, with the usual attitude towards feedback
Debunking the myth of unit files being significantly shorter than scripts used by all other init systems: A side-by-side look at run scripts and service units
Scope Creep Leads to Vulnerabilities
- systemd-resolved DNS cache poisoning
- To run systemd properly in container a FUSE LXCFS had to be created, and surely its own share of vulnerabilities:
- A Systemd Vulnerability Allows Attackers Hack Linux Machines via Malicious DNS response
Poor design
- Improper argument parsing
- systemd has a filename that starts with a hyphen! - This causes all sorts problems as it will usually be interpreted as the start of a command option when used on the command line. You don't even need to specify the filename for it to cause problems as it will affect commands that use globbing. Not to mention that the file in question, "-.slice", they refer to as the "root slice" which causes confusion as the term "slice" has been used for decades as an alternative way of referring to a disk partition yet their usage is completely unrelated.
- Systemd mounted efivarfs read-write, allowing motherboard bricking via 'rm' See also No POST after rm -rf / - Lennart's argument for mounting /sys/firmware/efi/efivars as read/write as a default behaviour doesn't hold water. Yes it's true that some tools may need to write to it but those tools are not needed for the general running of a system. efivars should not even be mounted as read-only by default. Those tools that need to write to efivars will generally only be invoked by a system administrator. A competent sysadmin will know how to mount efivars with read/write permissions when they need to to use those tools. The only reason to mount efivars by default is for convenience. This is by no means a good reason. From a security perspective, mounting efivars by default should be strongly discouraged as it breaks the principle of least privilege. Lennart goes on to state that systemd needs to write EFI variables. This demonstrates yet another example of scope creep and thus poor design.
- http://anonscm.debian.org/cgit/pkg-systemd/systemd.git/commit/?h=ubuntu&id=28640752854
- https://bugzilla.redhat.com/show_bug.cgi?id=1170765
- https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=784720
- https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=825394 "Now you can no longer expect a long running background processes to continue after logging out. For example, you can no longer start a screen or tmux session, log out, and expect to come back to it."
- https://www.freedesktop.org/wiki/Software/systemd/PredictableNetworkInterfaceNames/ systemd's predictable NIC names are actually unpredictable...
Ignorance of fundamental operating system concepts
- Lead systemd developer doesn't understand RAID or checksum
- Lead systemd developer doesn't understand su, expects it to do something else and then labels it a "broken concept" - su isn't supposed to inherit cgroups or audit, those concepts are relatively new and arrived well after the creation of su. TTYs were originally physical devices so of course su is supposed "inherit" the same device otherwise it would be truly broken. Pseudo TTYs emulate real TTYs so their behaviour is obviously expected to be identical. su really is just a simple mechanism that calls setuid(2) in order to switch to another user. If he needs to write a new utility to handle scenarios that su was never designed to handle, no problem, but to label it as a "broken concept" demonstrates a lack of understanding of what su actually is.